Zero Trust Security – Protecting Your Organization in the Modern Threat Landscape
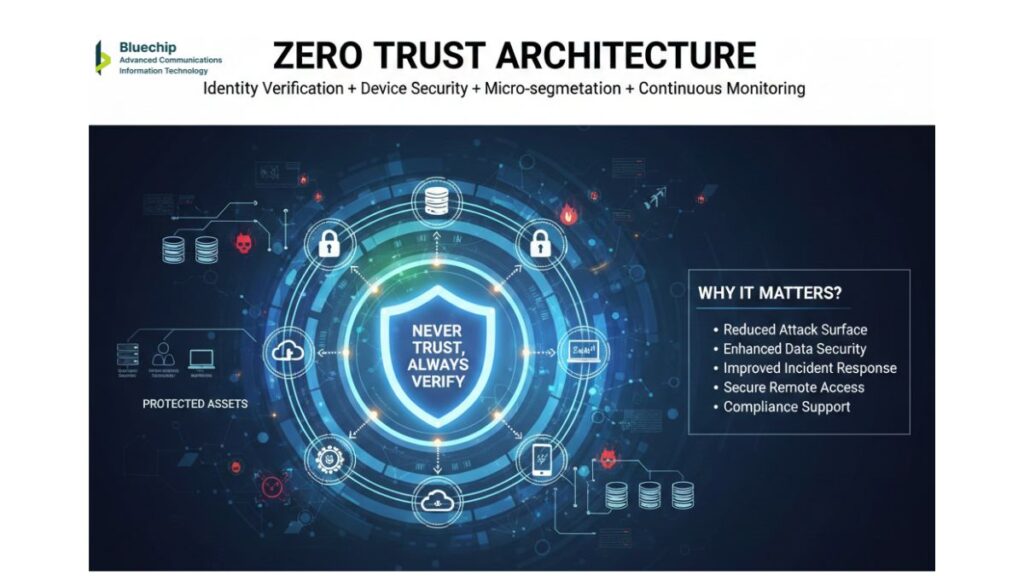
What Is Zero Trust Architecture and Why Does It Matter?
For decades, organizations built security around a simple concept: create a strong perimeter, and trust everything inside it. This approach made sense when employees worked in offices, data lived on company servers, and networks were clearly defined.
That world no longer exists.
Today, employees work from home, coffee shops, and traveling. Data lives in cloud services from multiple vendors. Partners access your systems. Contractors work alongside employees. The network perimeter has dissolved.
Zero trust security acknowledges this new reality. Rather than trusting everything inside a perimeter, zero trust assumes that every access request—whether from employees, partners, or systems—could be malicious. Every request must be verified, authenticated, and authorized before access is granted.
This isn’t paranoia. It’s realism based on breach patterns. Most successful attacks don’t come from outside the network. They come from compromised credentials used by someone who appears to have legitimate access.
How Zero Trust Architecture Works
Zero trust operates on a simple principle: never trust, always verify.
Every User Must Be Authenticated
Rather than trusting that someone is who they claim to be because they’re on the corporate network, zero trust requires continuous verification. This means multi-factor authentication—you must prove who you are through multiple means: something you know (password), something you have (phone), or something you are (biometric).
This isn’t just for initial login. Zero trust implements continuous authentication, verifying users throughout their session. If unusual behavior is detected (logging in from a new location, accessing resources at odd hours, trying to access systems they don’t normally use), additional verification is required or access is restricted.
Every Device Must Be Verified
The device you’re using to access corporate resources matters. Is it a company-managed computer with latest security patches? Or a personal device with unknown security status? Zero trust implementations verify that devices meet security standards—current operating system, active security software, encryption enabled—before allowing access to sensitive resources.
If a device doesn’t meet standards, it can still access basic resources, but not sensitive information. This encourages employees to use company-managed devices while providing flexibility for bring-your-own-device (BYOD) environments.
Network Location Is Irrelevant
Zero trust doesn’t care if you’re inside the corporate network or accessing from a coffee shop. Access controls are the same. This actually improves security because there’s no “trusted internal network” where security can be relaxed.
Access Is Based on Roles, Attributes, and Risk
Once users and devices are verified, access decisions are granular. Rather than “can access the network” (all-or-nothing), zero trust implements fine-grained controls:
Role-based access means your position determines what you can access. Finance managers see financial data. Engineering sees technical specifications. Sales sees customer information.
Attribute-based access considers multiple factors. Someone working in the office might have different access than someone working remotely. Someone accessing at 2 PM might have different access than someone accessing at 2 AM.
Risk-based access adjusts in real-time. If your account appears to be compromised, your access is restricted until you verify it’s really you.
Continuous Monitoring Detects Anomalies
Zero trust doesn’t just verify initial access. It monitors activity continuously. If a user is accessing resources they don’t normally use, it’s flagged. If data access patterns change dramatically, alerts are generated. If a system begins behaving unusually, it’s isolated.
This monitoring creates a detailed audit trail. If a breach occurs, investigators can see exactly what happened: which users accessed what, when, from where, and what data they viewed or downloaded.
Implementation Reality for Organizations
Zero trust sounds comprehensive, and it is. But implementing it doesn’t require replacing everything overnight.
Start with Critical Systems
Most organizations implement zero trust starting with the most sensitive systems: financial systems, intellectual property repositories, customer databases. Once these systems have zero trust controls, they expand to other systems.
Build on Existing Technology
You likely already have many components of zero trust. Active Directory provides user authentication. Firewalls control network access. Antivirus software ensures device security. Zero trust implementation often means integrating these existing systems and adding missing components.
Expect Some User Experience Impact
More verification means slightly more friction for users. An additional login factor takes ten seconds. Sometimes access is denied when users try to access systems outside their normal pattern. Organizations need to communicate why these additional steps exist and how they protect everyone.
The tradeoff is worth it. One incident involving compromised credentials costs far more than the minor inconvenience of additional verification.
Require Strong Governance
Zero trust requires governance—someone deciding which users need access to which systems, reviewing access rights regularly, and adjusting as roles change. This governance typically involves IT, Security, and the business functions that own the data being protected.
Benefits Beyond Security
While security is the primary benefit, zero trust implementations deliver additional value:
Better Compliance – Auditors love zero trust. The detailed logging and granular access controls demonstrate that your organization takes security seriously and can prove compliance with regulations.
Faster Incident Response – When a breach is suspected, zero trust implementations have complete audit trails. Rather than spending days investigating, you can quickly determine what happened and what data was accessed.
Reduced Lateral Movement – In a breach, attackers try to move from the compromised device to other systems. Zero trust makes this difficult. Even if one system is breached, segmentation prevents attackers from easily accessing others.
Business Enablement – Zero trust enables secure access to corporate resources from anywhere. This actually increases flexibility, allowing more remote work and partnership opportunities while maintaining security.
Zero Trust for Saudi Organizations
Saudi Arabia’s digital transformation goals and Vision 2030 objectives create specific requirements. Zero trust implementations help organizations:
Support Secure Digital Transformation – Vision 2030 initiatives require extensive digital capabilities. Zero trust provides the security foundation enabling confident digital expansion.
Meet NCA Requirements – The National Cybersecurity Authority requires demonstration of security controls. Zero trust’s detailed logging and audit trails support NCA compliance documentation.
Enable Critical Infrastructure Protection – Organizations managing critical infrastructure can implement zero trust to dramatically reduce breach risk.
Support Hybrid Workforce – With distributed workforces becoming permanent, zero trust enables secure access regardless of location or device.
The Path Forward
Zero trust isn’t a product you buy. It’s a security philosophy where every access decision is verified and monitored. Organizations that embrace this approach find that security becomes an enabler of business capability rather than just a constraint.
The question isn’t whether to implement zero trust. Organizations that don’t will eventually face breaches from compromised credentials or internal threats. The question is when to start and how quickly to implement. The sooner you begin, the sooner you achieve the security and operational benefits zero trust provides.
