What Is SASE? A Practical Guide for Businesses Rethinking Network Security
Network security used to be straightforward. You built a perimeter, put firewalls at the edge, and anyone inside the wall was trusted. That model worked when offices were fixed and all applications lived on local servers.
Today, that picture looks very different. Employees work from multiple locations. Applications run in the cloud. Devices connect from home networks, hotel Wi-Fi, and mobile connections. The old perimeter is gone — and so is the security logic built around it.
This is exactly the problem that SASE was designed to solve.
Quick Answer — What Is SASE?
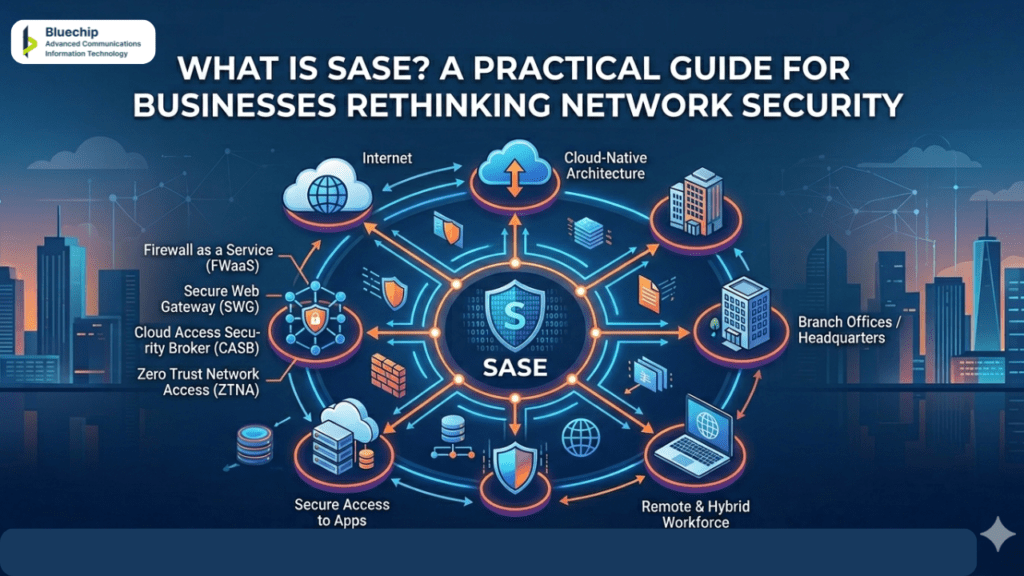
🔐 SASE (Secure Access Service Edge) is a network security framework that combines wide-area networking (WAN) with security functions — such as firewalling, secure web gateways, and identity verification — and delivers them together as a cloud-based service. |
Instead of routing traffic through a central data centre for inspection, SASE connects users securely and directly to the applications they need, wherever those applications are hosted. |
It is designed for organisations where users, devices, and data are distributed across many locations and cloud environments. |
What Does SASE Actually Mean?
SASE (Secure Access Service Edge) is a cloud-native architecture introduced by Gartner that converges two historically separate fields: networking and network security.
In traditional models, these functions were managed in silos with different tools and teams. SASE merges them into a single, unified service delivered from the cloud.
At its core is a Zero-Trust approach, meaning the network never assumes a user or device is safe based on location; instead, it continuously verifies identity and context before granting access.
The ‘edge’ in SASE represents a shift away from the central data centre, moving security and connectivity to wherever the user is—whether at home, in an office, or on the move.
The Core Components of a SASE Framework
A complete SASE architecture typically includes several integrated capabilities working together:
Software-Defined Wide Area Networking (SD-WAN)
SD-WAN allows organisations to manage and optimise how traffic flows across their network, connecting branch offices, remote workers, and cloud applications efficiently. It replaces older, rigid WAN connections with more flexible, software-controlled routing.
Zero Trust Network Access (ZTNA)
Zero trust is a security principle built on the idea that no user or device should be trusted automatically — even if they are already inside the corporate network. Every access request is verified, regardless of where it comes from.
In a SASE framework, zero trust network access means that users are granted access only to the specific applications they need, not the entire network. This significantly reduces the impact of a compromised account or device.
Cloud Access Security Broker (CASB)
A CASB acts as a security checkpoint between users and cloud applications. It monitors activity, enforces data policies, and flags unusual behaviour across cloud services — helping organisations maintain visibility even when employees work directly with external platforms.
Secure Web Gateway (SWG)
A secure web gateway filters internet traffic in real time, blocking access to malicious websites, preventing data leakage through web browsers, and enforcing acceptable use policies.
Firewall as a Service (FWaaS)
Instead of deploying physical firewalls at fixed network locations, FWaaS delivers firewall inspection and enforcement from the cloud — making it consistent across all users, wherever they connect from.
How SASE Differs from Traditional Network Security
To understand why SASE matters, it helps to compare it directly with the traditional approach.
Traditional Network Security | SASE Approach |
Perimeter-based trust model | Zero trust — verify every user, every time |
Traffic backhauled to central data centre | Traffic inspected at the cloud edge, near the user |
Separate tools for networking and security | Unified platform combining both functions |
Complex to manage across multiple sites | Centrally managed, consistent policy across all users |
Struggles to scale with remote work growth | Built for distributed workforces and cloud applications |
Zero Trust and SASE — How They Work Together
Zero trust is a principle; SASE is a framework that puts that principle into practice at scale.
When a user connects to a resource through a SASE-enabled network, the system does not simply ask “is this person inside the corporate perimeter?” Instead, it evaluates factors such as:
- Who is the user, and has their identity been verified?
- What device are they using, and does it meet security requirements?
- What application or resource are they requesting access to?
- Is this access request consistent with normal behaviour?
Only when these checks are satisfied is access granted — and even then, only to the specific resource requested, not the whole network.
This approach — often combined with identity and access management solutions and privileged access management controls — gives organisations much tighter control over who can reach sensitive systems and data.
Who Benefits Most from SASE?
SASE is particularly well-suited to:
- Organisations with a large remote or hybrid workforce
- Businesses running multiple applications across different cloud platforms
- Companies with branch offices or distributed teams across regions
- IT teams looking to simplify a fragmented security tool stack
- Organisations moving away from legacy VPN-based access models
It is less suited to very small organisations with a single fixed office, where simpler and more affordable tools may be a better fit.
Questions to Ask Before Choosing a SASE Solution
If you are evaluating SASE options, these questions can help you assess whether a solution genuinely meets your needs:
- Does the solution include both networking and security functions in a single platform, or are they loosely bundled?
- How does it handle identity verification and user authentication?
- Is zero trust network access built in, or an optional add-on?
- What visibility and reporting does it offer across users, devices, and applications?
- How does it integrate with the cloud platforms and applications you already use?
- What does deployment look like, and how much does it change your existing setup?
A reliable technology solutions provider will be able to walk you through these questions and help you compare options based on your specific environment.
Frequently Asked Questions (FAQ)
Item #1
Item #2
Item #3
If you are reviewing your organisation’s network security approach or comparing SASE solutions, speaking with an experienced technology solutions provider is a practical first step. A structured conversation about your current setup — including how your users connect, which applications you rely on, and where your biggest visibility gaps are — can help clarify which approach makes sense before you commit to any changes.
To understand how SASE and related network security solutions could apply to your environment, get in touch with the team.
