Cybersecurity and Network Security for Saudi Businesses
حلول الأمن السيبراني للمؤسسات – حماية عملك في المملكة العربية السعودية
Why Cybersecurity and Network Security Matter More Than Ever
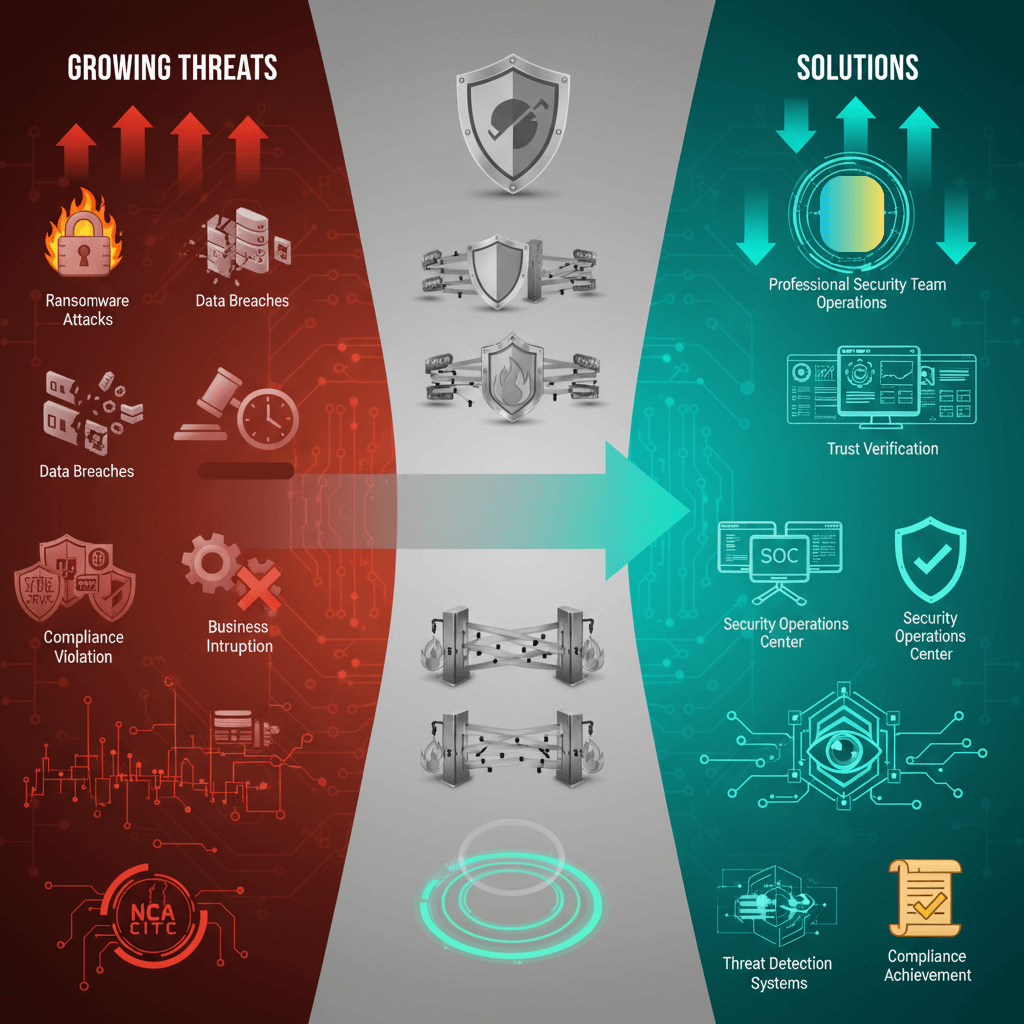
The Growing Threat Landscape
Organizations in Saudi Arabia face increasing cyber threats:
Ransomware Attacks – Up 400% in Middle East region
Data Breaches – Average cost exceeds $4 million globally
Regulatory Penalties – NCA compliance violations costly
Business Interruption – Downtime from attacks impacts revenue
Reputation Damage – Customer trust lost after breaches
في ظل التهديدات السيبرانية المتزايدة، أصبحت حلول الأمن السيبراني للمؤسسات ضرورة حتمية لضمان استمرارية الأعمال في المملكة العربية السعودية. تواجه الشركات السعودية اليوم تحديات معقدة تشمل هجمات الـRansomware، تسرب البيانات، ومتطلبات الهيئة الوطنية للأمن السيبراني (NCA) واللجنة الوطنية للاتصالات وتقنية المعلومات (CITC).
تقدم حلول الأمن السيبراني للمؤسسات حماية شاملة تشمل:
هندسة الأمان Zero Trust – لا ثقة، دائماً التحقق
مركز عمليات الأمن (SOC) – مراقبة 24/7 للتهديدات
إدارة الهوية والوصول – حماية الحسابات المميزة
إدارة الثغرات والرقع – منع الهجمات قبل حدوثها
حماية من فقدان البيانات – منع تسرب المعلومات الحساسة
تساعد هذه حلول الأمن السيبراني للمؤسسات الشركات السعودية على الامتثال لمعايير رؤية 2030، حماية البنية التحتية الحيوية، وتعزيز الثقة في البيئة الرقمية، مما يدعم نمو الأعمال بأمان في بيئة رقمية آمنة ومستقرة.
What IT professionals do?
Professional cyber security companies help organizations manage these growing threats through network security strategies and cyber security solutions.
Understanding Cyber Security vs. Network Security
الأمن السيبراني هو التخصص الأوسع الذي يحمي جميع الأصول الرقمية
What is the differnce?
Cyber security is the broader discipline protecting all digital assets:
Application security
Data protection
Endpoint security
Cloud security
User behavior monitoring
Network security specifically protects network infrastructure:
Firewalls and intrusion prevention
VPN and encrypted communications
Network segmentation
Traffic monitoring
Denial-of-service protection
Together, comprehensive cyber security and network security create robust defense.
Zero Trust Security – The Modern Approach to Network Security
What is Zero Trust and Why It Matters
Zero trust represents fundamental shift in security philosophy:
Traditional Approach: Trust internal network, secure perimeter
Zero Trust Approach: Never trust, always verify—every request
In zero trust architecture:
Every user authenticated and authorized
Every device verified before access
Every access monitored continuously
Least privilege access enforced
Microsegmentation isolates critical assets
Organizations implementing zero trust reduce breach impact by up to 80%.
Implementing Zero Trust in Your Organization
Leading cyber security companies implement zero trust through:
H4: Identity and Access Management
Multi-factor authentication everywhere
Continuous authentication refresh
Adaptive access policies
Risk-based access decisions
User behavior analytics
Privileged access management is especially critical—protecting accounts with highest privilege levels.
H4: Network Segmentation
Divide network into isolated segments
Control traffic between segments
Monitor all cross-segment communication
Restrict lateral movement after breach
Protect critical assets from widespread compromise
H4: Continuous Monitoring
Real-time visibility into all activity
Advanced analytics detect anomalies
Automated response to threats
Incident investigation capabilities
Compliance reporting
Comprehensive Cybersecurity Services from Leading Security Companies
Services Offered by Professional Cyber Security Companies
Top-tier cyber security companies provide:
Security Operations Center (SOC) Services
24/7 SOC monitoring provides:
Continuous threat detection
Incident response teams
Forensic investigation
Threat intelligence
Alert management
A dedicated SOC detects threats in real-time rather than days or weeks later.
Vulnerability Management and Patch Management
Continuous vulnerability identification and remediation:
Vulnerability management discovers weaknesses
Patch management applies fixes systematically
Risk-based prioritization
Compliance verification
Regulatory reporting
Unpatched systems cause majority of breaches.
Data Loss Prevention (DLP)
Data loss prevention prevents sensitive data exfiltration:
Monitor data in motion (network)
Monitor data at rest (storage)
Monitor data in use (endpoints)
Block unauthorized exfiltration
Provide audit trails
Critical for protecting intellectual property and customer data.
Incident Response and Forensics
When breaches occur, professional response minimizes damage:
Rapid containment
Investigation and evidence collection
Forensic analysis
Root cause determination
Remediation recommendations
Regulatory reporting support
Advanced Threat Detection and Prevention
Modern Threats Require Modern Solutions
Today’s threats are sophisticated and constantly evolving:
Malware and Ransomware Protection
Behavioral analysis identifies unknown malware
Machine learning detects anomalies
Sandboxing safely detects threats
Rapid response prevents spread
Backup systems enable recovery
Advanced Persistent Threats (APTs)
Sophisticated attackers remain undetected for months:
Threat hunting identifies hidden attackers
Lateral movement detection
Command and control detection
Long-term monitoring
Attacker infrastructure analysis
Email Security
Email is primary attack vector:
Advanced email filtering
URL and attachment scanning
Anti-phishing detection
Email encryption
User awareness training
Compliance and Regulatory Requirements
Meeting Saudi Arabia’s Cybersecurity Requirements
Organizations must meet multiple compliance frameworks:
NCA (National Cybersecurity Authority) Compliance
Essential controls requirements
Incident reporting obligations
Annual compliance certification
Continuous monitoring requirements
Executive accountability
Cyber security companies help organizations achieve and maintain NCA compliance.
CITC Requirements
Telecommunications security standards
Data localization requirements
Encryption standards
Access logging requirements
Audit trail maintenance
Vision 2030 Digital Security Goals
Support national digital transformation safely
Protect critical infrastructure
Build domestic cybersecurity capability
Develop regional expertise
Enable trusted digital economy
Choosing the Right Cybersecurity Company
What to Look For in Cyber Security Companies
When selecting cyber security companies:
Certifications and Credentials
ISO 27001 (Information Security Management)
SOC 2 Type II (Service Organization Controls)
CISSP (Certified Information Systems Security Professional)
CEH (Certified Ethical Hacker)
GCIH (GIAC Certified Incident Handler)
Relevant Experience
Years in cybersecurity (15+ preferred)
Experience with organizations your size
Industry-specific expertise
Successful incident response cases
Certifications in key technologies
Technology and Tools
Advanced SIEM (Security Information and Event Management)
Threat intelligence integration
Automation and orchestration
AI-powered analytics
Cloud security expertise
Support and Service Levels
24/7/365 availability
Response time commitments
Dedicated teams
Executive reporting
Proactive threat hunting
The Future of Cybersecurity
Emerging Threats and Solutions
The cybersecurity landscape continues evolving:
AI-Powered Attacks and Defenses
Attackers using AI to automate attacks
Defenders using AI for threat detection
Arms race in AI capabilities
New threat vectors emerging
Continuous adaptation required
Quantum Computing Threat
Quantum computers will break current encryption
Organizations must prepare now
Post-quantum cryptography migration
Key management evolution
Long-term security strategy
IoT and Edge Device Security
Billions of IoT devices creating security challenges
Limited security on many devices
Network-level security critical
Monitoring and segmentation essential
Emerging attack surfaces
Conclusion – Making Cybersecurity Investment Priority
In today’s threat landscape, cyber security is not optional—it’s essential. Whether implementing zero trust architecture, establishing network security controls, or partnering with cyber security companies for managed services, organizations must treat security as strategic priority rather than just technical requirement.
